|
Cybercriminals distribute it by means of malspam. GIBON is attached to the malicious office document that contains macros. Once enabled, macros will download and install GIBON virus on the victim’s computer.
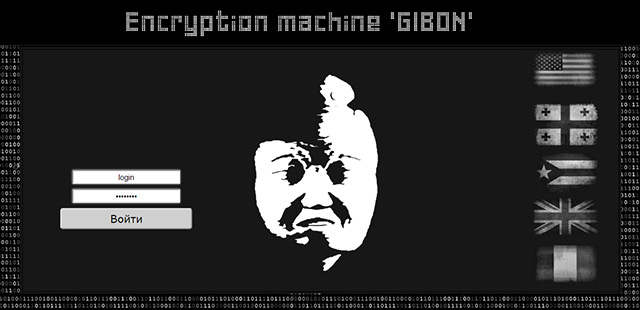
Whenever a new extortion virus appears, it is hard to come up with a name for it. Sometimes malware authors give you clues, other times security researchers use strings present inside the executable.
With the ransomware in question, cybercriminals put the name in two places. The user agent includes the GIBON string when it communicates with the C&C server. The second place is the Admin panel. One can clearly read: "Encryption
machine GIBON".
Once installed and launched GIBON connects to the C&C server and sends a base64 code string which includes the version of Windows and the timestamp. This way it registers new victims. After that, the C&C server also responds
with a base64 string that is a ransom note. Hacker can update the ransom note content at any time.
After user registration, the ransomware generates a crypto key and sends to the server. The key is needed to lock the files.
Now the GIBON Ransomware is ready to start the encryption process. GIBON encrypts all types of files regardless of their extension and location. There is only one exception GIBON does not encrypt files in the Windows folder.
While encrypting the data files, ransomware adds the .encrypt extension to the file name.
Each folder that contains encrypted files will also receive a ransomware note called READ_ME_NOW.txt. It demands that infected users contact the ransomware author at yourfood20@mail.ru or bomboms123@mail.ru to
receive further payment instructions.
It is strange but GIBON ransom notes do not include the ransom amount to be paid. Victims should find it after getting in touch with the hacker.
Michael Gillespie studied GIBON and managed to find the way to decrypt it. In case you are infected, you can find the decryptor here.
|