|
Figuratively speaking, Cerber is a reincarnation of a well-known scary mythological creature, only in 1’s and 0’s. This is a widespread strain of crypto ransomware that causes a great deal of trouble to the infected Windows users.
The main challenge that its victims face is all about regaining access to their files, because the infection blatantly encrypts the data using AES-256, a high-entropy subtype of the Advanced Encryption Standard. This is a symmetric
cryptosystem with one key for both the encoding and decoding task.
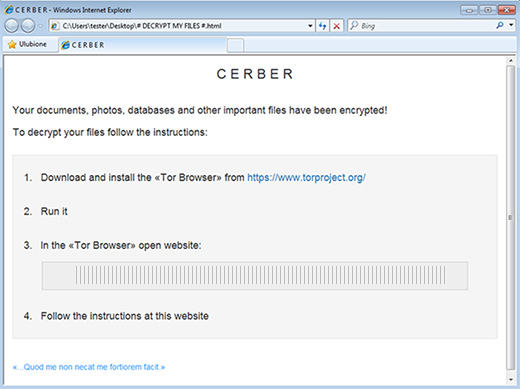
Here are some conspicuous attributes of the Cerber Trojan compromise: it creates three avenues for ransom payment and recovery in the form of # Decrypt My Files #.htm, # Decrypt My Files #.txt, and # Decrypt My Files #.vbs; it
appends the encrypted files with the .cerber extension; and it requires 1.25 Bitcoins, or around $500, to release the hostage data.
The VBScript version of ransom notes mentioned above makes Cerber a one-of-a-kind threat. When this file is opened, it automatically generates a creepy audio message about the attack and the basic steps to restore the personal
information. There isn’t much complexity and sophistication in this, but it’s a new thing on the ransomware arena.
Computer users end up falling victim to this crimeware when they visit a hacked website that redirects them to an exploit kit’s landing page. From there, a piece of malicious code connects to the machine, finds unpatched software
and exploits the loopholes in such programs to inject the ransomware in a stealthy way. One more vector that the malefactors use to serve their infection is through phishing, where users are duped into opening a harmful email
attachment.
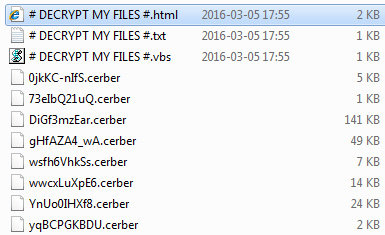
Cerber scans the hard drive and mapped network shares for hundreds of data types once it trespasses on a computer system. When it finds a match, it encrypts an object, renames it to something like gHfAZA4E6.cerber, and drops the
# Decrypt My Files # instructions combo into the folder where the file resides. When sticking to the imposed steps, the victim is encouraged to download and install the Tor Browser and open an .onion gateway indicated in the
ransom notes. The Tor page features a language selection option and provides a countdown clock displaying the time left before the ransom size doubles. In addition, it contains a Bitcoin address to which the user is to submit
the buyout.
According to recent security reports, this Trojan adds the contaminated machines to a botnet, so it takes advantage of every infection instance even if the user refuses to pay up. By zombifying PCs, the Cerber ransomware operators
can pull off distributed denial-of-service (DDoS) attacks against organizations, which indirectly makes the computer owner an accomplice. This fact, along with the abominable ransom demands and the unavailability of personal
data, makes this sample a must-avoid pest.
How to recover .cerber files without submitting the ransom
A brief disclaimer: the techniques described below do not actually decrypt the locked data. Instead, they provide viable workarounds for exploiting probable imperfections of the way that this virus implements the crypto and handles
the victim’s files. Although it’s premature to assert whether or not these tips will do the trick in your situation, nothing more efficient has been invented to date. Without further ado, peruse the following methods to mitigate
the harm from the ransomware compromise.
-
Use Volume Shadow Copy Service (VSS) to your advantage
In case you didn’t know, Shadow Copies represent Microsoft Windows’ feature for file backup. The operating system makes point-in-time snapshots of files over the course of critical updates and the creation of System Restore
points. Normally, the Cerber ransom Trojan disables VSS on early stages of the attack, but chances are it fails to.
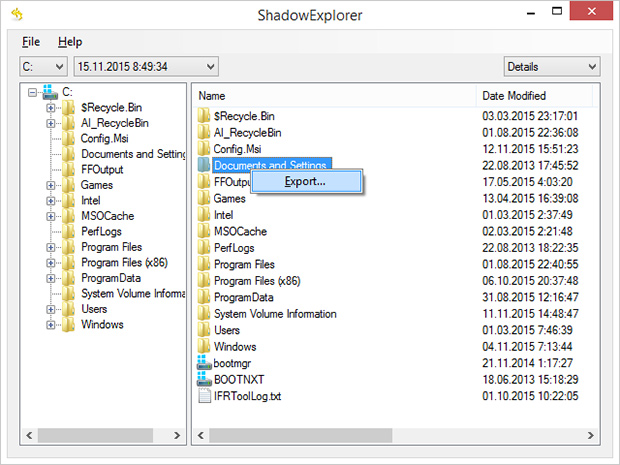
Nevertheless, it certainly won’t hurt to try this: for a start, download and install
Shadow Explorer
app. It is a free solution that displays the file hierarchy in a user-friendly way and automates the process of retrieving the previous versions of files and folders. You can easily export data by right-clicking the object
of interest and selecting the corresponding option as shown on the picture below.
-
Try data recovery software
These types of solutions were originally designed for forensic purposes as well as to restore the information that was obliterated accidentally or due to hardware failures. Their scope of use has expanded with the emergence
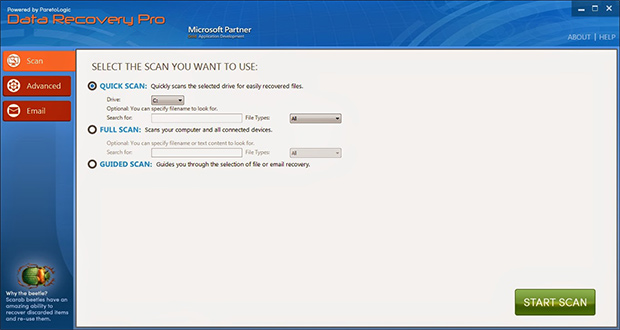
of cryptographic infections like Cerber. Again, this isn’t a cure-all, but it may help under certain circumstances. So go ahead and download ParetoLogic’s Data Recovery Pro, have your computer scanned for recoverable
data and follow the program’s directions to proceed with the file rescue activity.
-
Use backups, they’re indispensable
Nothing beats backups when ransomware attacks your computer. No matter if your files are backed up to an external piece of hardware or a cloud provider, everything can be downloaded back to the machine in a few clicks. Just
make sure you have removed the ransomware before retrieving the data, otherwise the crypto routine will repeat.
Prevent ransomware attacks further on
In order to be a moving target for crypto malware like Cerber, it’s strongly recommended to patch potentially vulnerable software (Adobe Flash Player, Java) on a regular basis, refrain from opening fishy email attachments, keep
macros in Microsoft Office documents disabled, use a dependable antimalware suite, and of course maintain secure backups of the most valuable files.
|