|
Almost like regular computer applications, crypto ransomware gets regular updates aimed at patching vulnerabilities and improving performance. This fact showcases how well-orchestrated the present-day cyber extortion campaigns
are. The malefactors in charge, obviously, analyze the efficiency of what they do over a certain period of time and, based on this assessment, adjust their activity to new challenges. An example is the Locky virus update that
took place a few days ago. This is the third time its code has gotten modified since February 2016. It’s hard to call the latest instance a code revamp, but there are conspicuous changes. For instance, the infection now concatenates
the .odin extension to scrambled files rather than .zepto. Also, the names of documents with a roadmap on data recovery have been altered to _HOWDO_text.htm and _HOWDO_text.bmp.
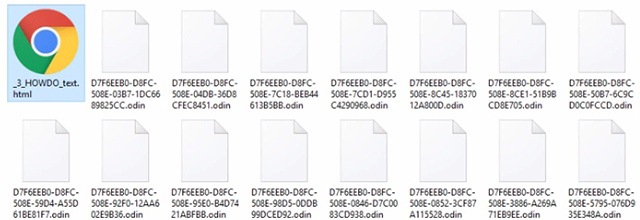
Aside from the above-mentioned modifications, the Odin ransomware retains most of the previous Locky patterns. Its authors probably realize it makes no sense changing something that already works. The way the new iteration treats
its victims’ files is it makes filenames morph into strings of 32 random numbers and digits. As a result, an arbitrary entry turns into a lengthy array like D7F6EEB0-D8FC-508E-59D4-B4D7421ABFBB.odin. It doesn’t take a genius
to understand that locating, say, an invaluable photo by such a name is unfeasible. Therefore, even if a contaminated user applies for professional tech assistance to try and restore one important item, it’s going to be no go.
Instead, they’ll most likely have to peruse the instructions provided by the ransom Trojan.
The preliminary recovery steps are explicated in documents named _HOWDO_text.htm (.bmp). These notes are easy to find – the offending program adds them to the desktop as well as to every folder with jumbled files. Furthermore,
the ransomware replaces the desktop wallpaper with an image containing these directions. The warning says, “All of your files are encrypted with RSA-2048 and AES-128 ciphers,” and lists several URLs to visit over Tor Browser.
The landing site titled “Locky Decryptor Page” contains the ransom size (0.5 BTC) and a Bitcoin address to submit it. Although paying the ransom may be the only option to get files back in most cases, any alternative workarounds
are worth a shot. By following some of the recommendations below, you may be able to restore the locked data.
How to recover .odin files without submitting the ransom
A brief disclaimer: the techniques described below do not actually decrypt the locked data. Instead, they provide viable workarounds for exploiting probable imperfections of the way that this virus implements the crypto and handles
the victim’s files. Although it’s premature to assert whether or not these tips will do the trick in your situation, nothing more efficient has been invented to date. Without further ado, peruse the following methods to mitigate
the harm from the ransomware compromise.
-
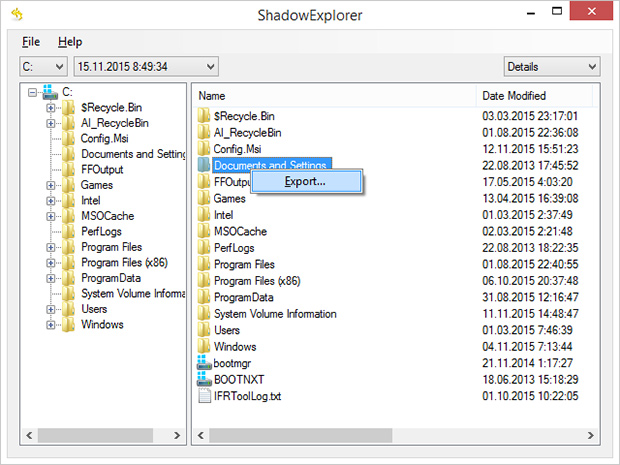
Use Volume Shadow Copy Service (VSS) to your advantage
In case you didn’t know, Shadow Copies represent Microsoft Windows’ feature for file backup. The operating system makes point-in-time snapshots of files over the course of critical updates and the creation of System Restore
points. Normally, the Zepto ransom Trojan disables VSS on early stages of the attack, but chances are it fails to.
Nevertheless, it certainly won’t hurt to try this: for a start, download and install
Shadow Explorer
app. It is a free solution that displays the file hierarchy in a user-friendly way and automates the process of retrieving the previous versions of files and folders. You can easily export data by right-clicking the object
of interest and selecting the corresponding option as shown on the picture below.
-
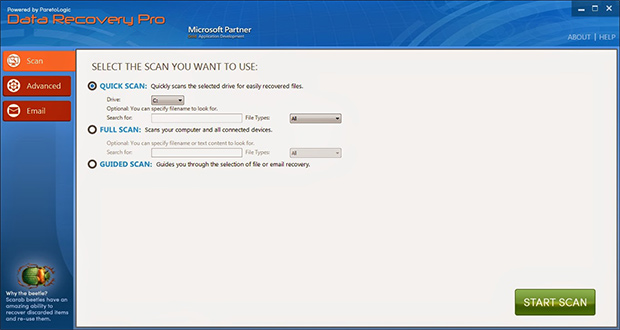
Try data recovery software
These types of solutions were originally designed for forensic purposes as well as to restore the information that was obliterated accidentally or due to hardware failures. Their scope of use has expanded with the emergence
of cryptographic infections like Odin. Again, this isn’t a cure-all, but it may help under certain circumstances. So go ahead and download ParetoLogic’s Data Recovery Pro, have your computer scanned for recoverable
data and follow the program’s directions to proceed with the file rescue activity.
-
Use backups, they’re indispensable
Nothing beats backups when ransomware attacks your computer. No matter if your files are backed up to an external piece of hardware or a cloud provider, everything can be downloaded back to the machine in a few clicks. Just
make sure you have removed the ransomware before retrieving the data, otherwise the crypto routine will repeat.
Prevent ransomware attacks further on
In order to be a moving target for crypto malware like Odin, it’s recommended to patch potentially vulnerable software (Adobe Flash Player, Java) on a regular basis, refrain from opening fishy email attachments, keep macros in
Microsoft Office documents disabled, use a dependable antimalware suite, and of course maintain secure backups of the most valuable files.
|