|
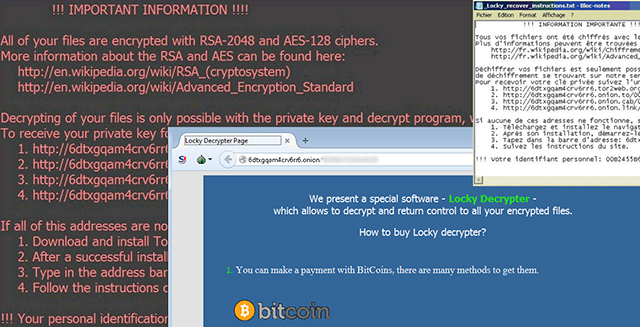
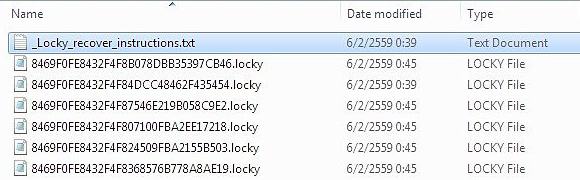
When the crypto virus called Locky attacks a computer, things get out of hand. Not only does this nasty infection deny the availability of the user’s proprietary data, but it also renders files completely unrecognizable. It substitutes
filenames with long strings of letters and characters and concatenates the .locky extension to each. In order to revert this bad impact, victims are told to pay somewhere in the range of 0.5 Bitcoins, or around $250 based on
the current exchange rate. The documents named "_Locky_recover_instructions.txt" and "_Locky_recover_instructions.bmp" provide the users with a walkthrough to recover from the attack and get the frozen files back. By the way,
the BMP variant replaces the original desktop wallpaper.
The distributors of Locky ransomware have been leveraging a contamination scheme that cannot boast much innovation or hi-tech characteristics whatsoever. They use Microsoft Word macros. The idea is as follows: a user sees a new
message in their inbox, gets curious, opens it and discovers that it has an enclosed invoice. Once the person opens the document, its contents don’t make sense and look like a Chinese puzzle. But then, lo and behold, a prompt
appears at the top of the window that says enabling macros will fix the bug and make the text readable. However, what happens in fact is the attackers use a catalogued macro vulnerability to embed the ransom Trojan into the OS.
Locky traverses the local drives, mapped and unmapped network shares, as well as removable media in search of the victim’s personal documents, images, videos, presentations, databases and other popular types of data. As soon as
the list of targeted objects is readily available, the ransomware utilizes the RSA-2048 cryptosystem in order to encrypt the files. As mentioned above, filenames are subject to critical changes, too.
The _Locky_recover_instructions.txt (.bmp) ransom notes provide the user with their personal ID and several alternate Tor links to the Locky Decrypter Page. The victim is supposed to use this page to submit the 0.5 BTC ransom
and download the decrypt tool once the scammers have verified and confirmed the payment. Although security gurus haven’t yet created a solution to decrypt files hijacked by Locky, there do exist techniques that might lend you
a helping hand in the recovery activity.
How to recover .locky files without submitting the ransom
A brief disclaimer: the techniques described below do not actually decrypt the locked data. Instead, they provide viable workarounds for exploiting probable imperfections of the way that this virus implements the crypto and handles
the victim’s files. Although it’s premature to assert whether or not these tips will do the trick in your situation, nothing more efficient has been invented to date. Without further ado, peruse the following methods to mitigate
the harm from the ransomware compromise.
-
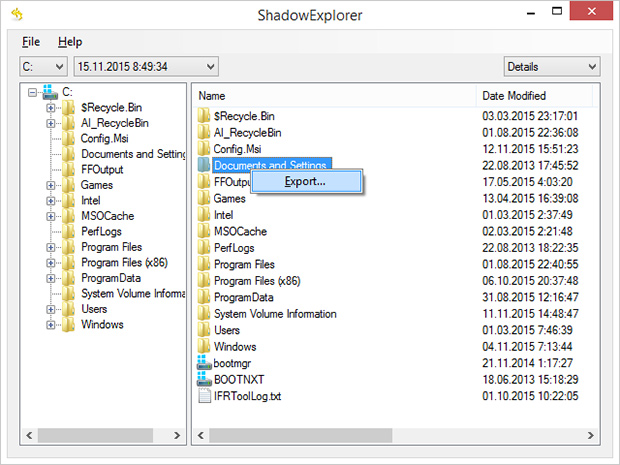
Use Volume Shadow Copy Service (VSS) to your advantage
In case you didn’t know, Shadow Copies represent Microsoft Windows’ feature for file backup. The operating system makes point-in-time snapshots of files over the course of critical updates and the creation of System Restore
points. Normally, the Locky ransom Trojan disables VSS on early stages of the attack, but chances are it fails to.
Nevertheless, it certainly won’t hurt to try this: for a start, download and install
Shadow Explorer
app. It is a free solution that displays the file hierarchy in a user-friendly way and automates the process of retrieving the previous versions of files and folders. You can easily export data by right-clicking the object
of interest and selecting the corresponding option as shown on the picture below.
-
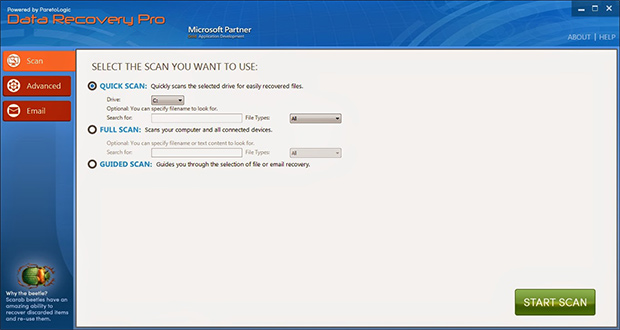
Try data recovery software
These types of solutions were originally designed for forensic purposes as well as to restore the information that was obliterated accidentally or due to hardware failures. Their scope of use has expanded with the emergence
of cryptographic infections like Locky. Again, this isn’t a cure-all, but it may help under certain circumstances. So go ahead and download ParetoLogic’s Data Recovery Pro, have your computer scanned for recoverable
data and follow the program’s directions to proceed with the file rescue activity.
-
Use backups, they’re indispensable
Nothing beats backups when ransomware attacks your computer. No matter if your files are backed up to an external piece of hardware or a cloud provider, everything can be downloaded back to the machine in a few clicks. Just
make sure you have removed the ransomware before retrieving the data, otherwise the crypto routine will repeat.
Prevent ransomware attacks further on
In order to be a moving target for crypto malware like Locky, it’s strongly recommended to patch potentially vulnerable software (Adobe Flash Player, Java) on a regular basis, refrain from opening fishy email attachments, keep
macros in Microsoft Office documents disabled, use a dependable antimalware suite, and of course maintain secure backups of the most valuable files.
|