|
What makes an arbitrary sample of ransomware an uncrackable infection is a flawless take on cryptography. These threats can only get ransoms flowing in as long as victims’ files are scrambled according to the best encryption practices.
Both the Cerber virus and its recently updated version called Cerber2 share the same crypto approach, where one’s data undergoes processing with AES-256, a symmetric cipher generating a secret key that doesn’t touch the compromised
computer at all. To restore these personal documents, images, videos and databases, the infected person needs the key but won’t obtain it unless they submit around 1.5 Bitcoins to the threat actors within 5 days. The concomitant
attributes of this plague include the .cerber2 extensions appended to filenames, as well as ransom notes named # Decrypt My Files # spawned all over the PC’s data hierarchy.
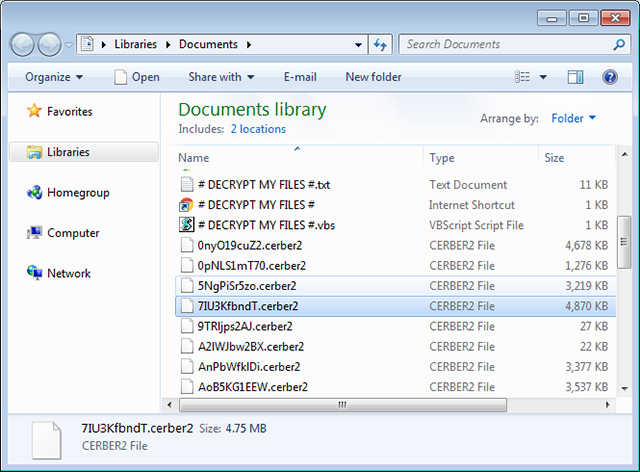
The above-mentioned recovery instructions come in three editions, namely # Decrypt My Files #.txt, # Decrypt My Files #.htm, and # Decrypt My Files #.vbs. Their purpose is to provide the victim with a road map on retrieving their
encrypted data. In particular, the user is required to download and install the Tor Browser Bundle for anonymous interaction with the campaign’s Command and Control server, open a specific website in it, and buy the piece of
software called the “Cerber Decryptor”. The 5-day payment deadline isn’t a data termination point, but the ransom ends up increasing to 3 Bitcoins afterwards.
The names of the victim’s proprietary files are tweaked beyond simply the concatenation of .cerber2 tail. The ransomware also randomizes the original strings, replacing each one with 10 hexadecimal characters. Ergo, a graphics
file named “cat.bmp” turns into something like A2u3nbDTio.cerber2.
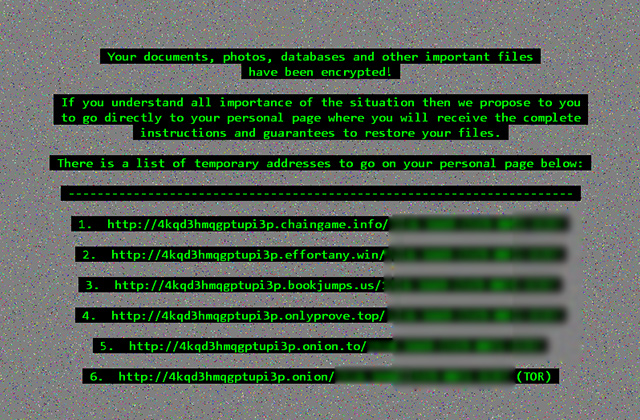
Yet another spooky side effect of this assault is the desktop background set by the ransomware. It is a mosaic of numerous variegated dots, with green text at the forefront. The message is to inform the user that their important
files have been encrypted and provide 6 temporary Tor addresses to their personal page. As it has been mentioned, the developers of Cerber2 implemented the Advanced Encryption Standard correctly, therefore all recovery efforts
via breaking the crypto are mostly futile. Whereas researchers are still struggling to contrive a free decryptor, the infected people are bound to pay up to the scammers or leverage the conventional forensics methodology to get
their data back. Sometimes things like Shadow Copies or specially crafted file recovery tools can do the trick. The most reliable avenue, though, is to restore data from a backup storage if it’s being maintained.
How to recover .cerber2 files without submitting the ransom
A brief disclaimer: the techniques described below do not actually decrypt the locked data. Instead, they provide viable workarounds for exploiting probable imperfections of the way that this virus implements the crypto and handles
the victim’s files. Although it’s premature to assert whether or not these tips will do the trick in your situation, nothing more efficient has been invented to date. Without further ado, peruse the following methods to mitigate
the harm from the ransomware compromise.
-
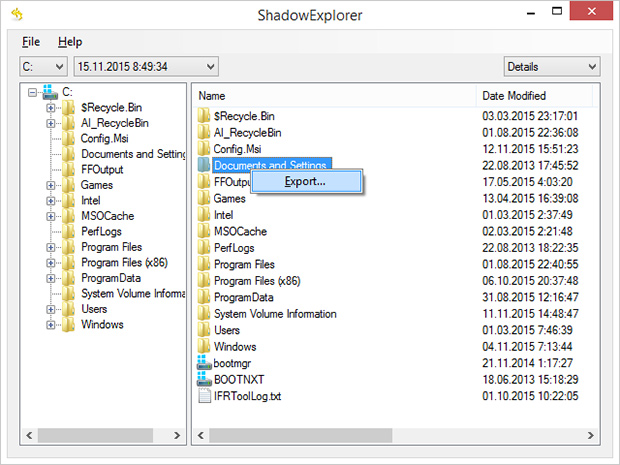
Use Volume Shadow Copy Service (VSS) to your advantage
In case you didn’t know, Shadow Copies represent Microsoft Windows’ feature for file backup. The operating system makes point-in-time snapshots of files over the course of critical updates and the creation of System Restore
points. Normally, the Cerber2 ransom Trojan disables VSS on early stages of the attack, but chances are it fails to.
Nevertheless, it certainly won’t hurt to try this: for a start, download and install
Shadow Explorer
app. It is a free solution that displays the file hierarchy in a user-friendly way and automates the process of retrieving the previous versions of files and folders. You can easily export data by right-clicking the object
of interest and selecting the corresponding option as shown on the picture below.
-
Try data recovery software
These types of solutions were originally designed for forensic purposes as well as to restore the information that was obliterated accidentally or due to hardware failures. Their scope of use has expanded with the emergence
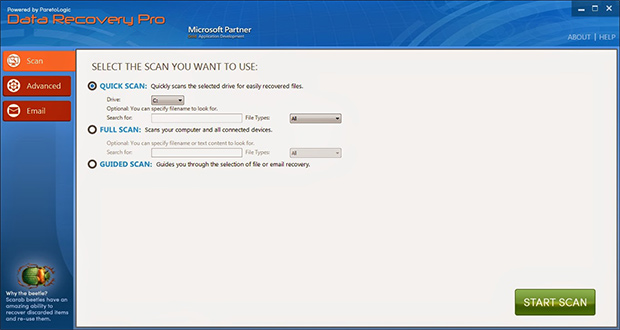
of cryptographic infections like Cerber2. Again, this isn’t a cure-all, but it may help under certain circumstances. So go ahead and download ParetoLogic’s Data Recovery Pro, have your computer scanned for recoverable
data and follow the program’s directions to proceed with the file rescue activity.
-
Use backups, they’re indispensable
Nothing beats backups when ransomware attacks your computer. No matter if your files are backed up to an external piece of hardware or a cloud provider, everything can be downloaded back to the machine in a few clicks. Just
make sure you have removed the ransomware before retrieving the data, otherwise the crypto routine will repeat.
Prevent ransomware attacks further on
In order to be a moving target for crypto malware like Cerber2, it’s strongly recommended to patch potentially vulnerable software (Adobe Flash Player, Java) on a regular basis, refrain from opening fishy email attachments, keep
macros in Microsoft Office documents disabled, use a dependable antimalware suite, and of course maintain secure backups of the most valuable files.
|