|
Crypt0L0cker, alias TorrentLocker, is a cryptography-backed infection that takes victims’ personal data hostage. Referred to as ransomware, this category of malicious code has been at the very apex of computer threat landscape
for years. The perpetrating program under analysis contaminates Windows machines via booby-trapped email attachments that look interesting enough for recipients to open them. When inside, Crypt0L0cker scans the local hard drive,
removable media and network drives for widespread types of files. This scan runs in the background, so there isn’t much chance that the user takes notice of it. The ransomware skips files that are necessary for stability of the
operating system, including ones with the .exe, .dll, .cmd, .scr, .lnk, .sys, .bat, .msi, .ico, .ini and some others. This is a smart move as it allows the extortion cycle to go all the way.
Earlier iterations of Crypt0L0cker would concatenate the .enc or .encrypted extension to every data entry that underwent the enciphering. The variant currently in rotation has a different take on this file labeling. It uses extensions
consisting of six random characters. Moreover, every single scrambled file gets a unique string appending it. For instance, two sample files Article.docx and Sunrise.jpg will turn into something like Article.docx.biqxtu and Sunrise.jpg.oynadx,
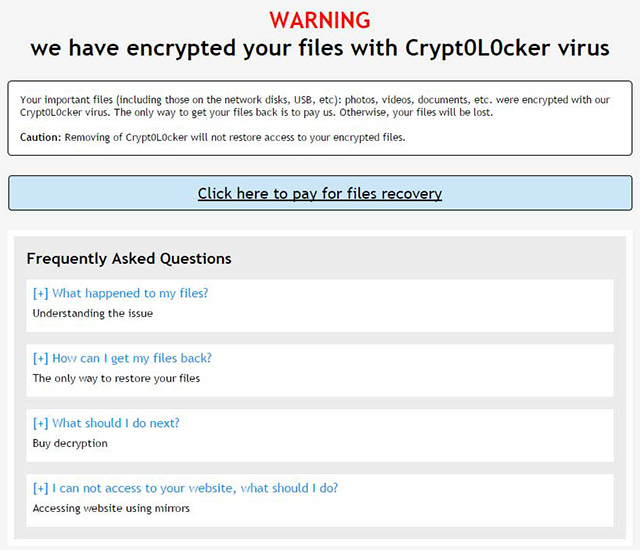
respectively. An arbitrary folder with these messed-up files will also contain two editions of ransom notes. One is called HOW_TO_RESTORE_FILES.htm and HOW_TO_RESTORE_FILES.txt. The alert part in them says, “Warning, we have
encrypted your files with Crypt0L0cker virus. Your important files (including those on the network disks, USB, etc.): photos, videos, documents, etc. were encrypted with our Crypt0L0cker virus. The only way to get your files
back is to pay us. Otherwise, your files will be lost.”
This combo of documents isn’t only about telling the victim what happened. They are also decryption how-to’s instructing the infected users to install Tor browser and visit their personal page titled “Buy Decryption”. The page
provides the amount of the ransom payable in cryptocurrency, the Bitcoin address to submit it, and the deadline for paying up. The price of full recovery is usually about 0.5 BTC, and it doubles in five days. Security analysts
have been trying hard to defeat Crypt0L0cker’s encryption, to no avail. Under the circumstances, if you are infected with this nasty virus, consider trying several workarounds that have helped ransomware victims reinstate their
data without sending the ransom to crooks.
How to recover Crypt0L0cker-encrypted files without submitting the ransom
A brief disclaimer: the techniques described below do not actually decrypt the locked data. Instead, they provide viable workarounds for exploiting probable imperfections of the way that this virus implements the crypto and handles
the victim’s files. Although it’s premature to assert whether or not these tips will do the trick in your situation, nothing more efficient has been invented to date. Without further ado, peruse the following methods to mitigate
the harm from the ransomware compromise.
-
Use Volume Shadow Copy Service (VSS) to your advantage
In case you didn’t know, Shadow Copies represent Microsoft Windows’ feature for file backup. The operating system makes point-in-time snapshots of files over the course of critical updates and the creation of System Restore
points. Normally, the Zepto ransom Trojan disables VSS on early stages of the attack, but chances are it fails to.
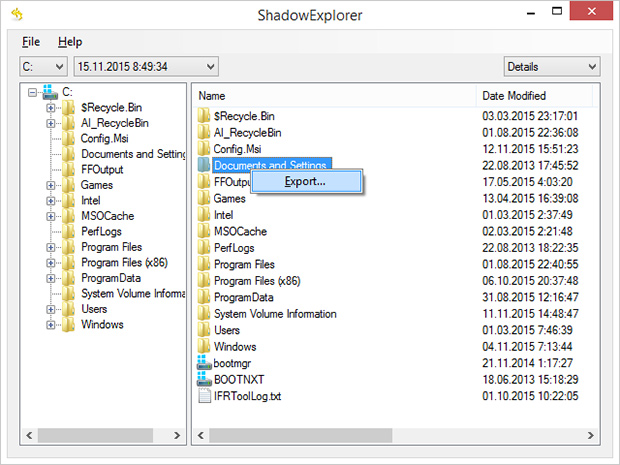
Nevertheless, it certainly won’t hurt to try this: for a start, download and install
Shadow Explorer
app. It is a free solution that displays the file hierarchy in a user-friendly way and automates the process of retrieving the previous versions of files and folders. You can easily export data by right-clicking the object
of interest and selecting the corresponding option as shown on the picture below.
-
Try data recovery software
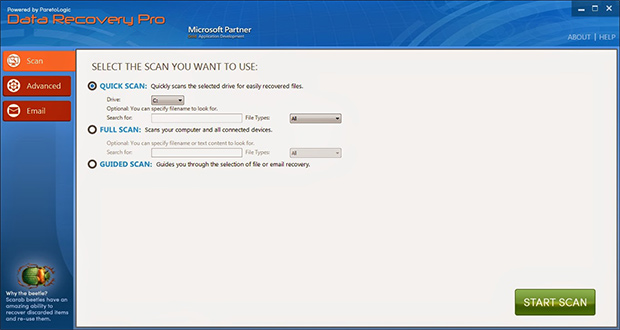
These types of solutions were originally designed for forensic purposes as well as to restore the information that was obliterated accidentally or due to hardware failures. Their scope of use has expanded with the emergence
of cryptographic infections like Crypt0L0cker. Again, this isn’t a cure-all, but it may help under certain circumstances. So go ahead and download ParetoLogic’s Data Recovery Pro, have your computer scanned
for recoverable data and follow the program’s directions to proceed with the file rescue activity.
-
Use backups, they’re indispensable
Nothing beats backups when ransomware attacks your computer. No matter if your files are backed up to an external piece of hardware or a cloud provider, everything can be downloaded back to the machine in a few clicks. Just
make sure you have removed the ransomware before retrieving the data, otherwise the crypto routine will repeat.
Prevent ransomware attacks further on
In order to be a moving target for crypto malware like Crypt0L0cker, it’s recommended to patch potentially vulnerable software (Adobe Flash Player, Java) on a regular basis, refrain from opening fishy email attachments, keep macros
in Microsoft Office documents disabled, use a dependable antimalware suite, and of course maintain secure backups of the most valuable files.
|